Ransomware has moved from a hypothetical threat to a statistical inevitability for South African businesses. With the country ranking as the most targeted nation in Africa for ransomware and infostealer attacks in late 2024, the question is no longer if an attack will occur, but when.
For IT managers and security architects, the focus must shift from pure prevention to rapid detection and response. Understanding how cybersecurity systems operate in practice during a live attack can mean the difference between a minor disruption and a catastrophic data breach.
Related articles:
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
The Kill Chain: How Ransomware Strikes
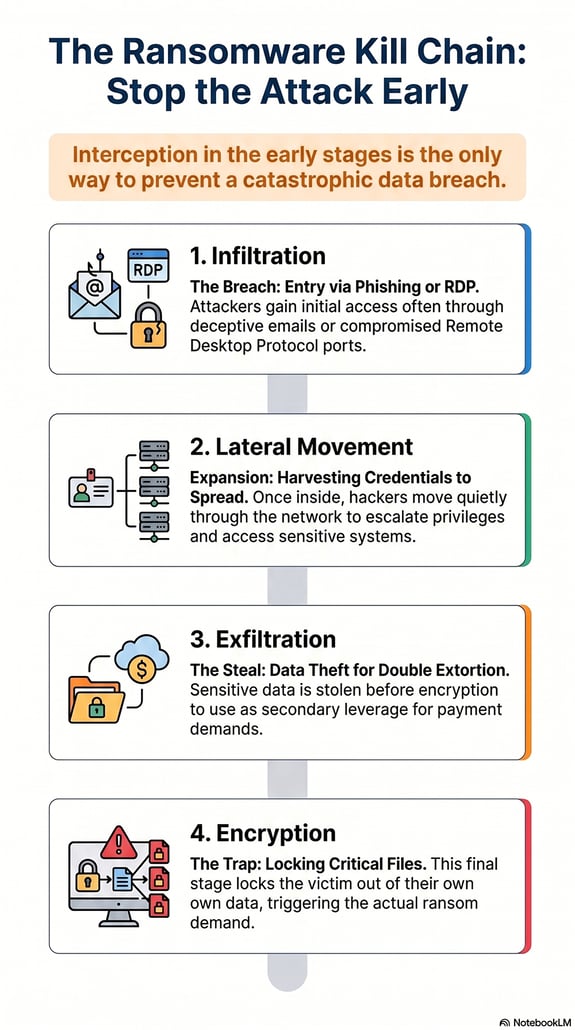
Modern ransomware is rarely a "smash and grab" event. It is a calculated process often described as the "Cyber Kill Chain".
- Infiltration: Attackers gain entry, often via phishing emails or compromised Remote Desktop Protocol (RDP) ports.
- Lateral Movement: They quietly move through the network, harvesting credentials and escalating privileges.
- Exfiltration: Before encryption, they steal sensitive data to use as leverage (double extortion).
- Encryption: Finally, the trap is sprung, locking critical files and demanding payment.
Effective defence requires intercepting the attacker during the first three steps, long before the encryption phase begins.
Detection: Looking for Anomalies
Silence is the enemy. By the time a ransom note appears on a screen, the battle is largely lost. Early detection relies on spotting subtle anomalies in network behaviour.
- Endpoint Detection and Response (EDR): Modern EDR tools monitor individual devices for suspicious processes, such as PowerShell scripts attempting to disable backups or uninstall antivirus software.
- Honeypots: These are decoy servers or files left intentionally vulnerable. If a user accesses them, it triggers an immediate high-priority alarm, as no legitimate employee would have reason to touch them.
- User Behaviour Analytics (UBA): This technology establishes a "baseline" of normal activity. If a finance officer’s account suddenly starts downloading gigabytes of data at 3 AM, UBA flags this as an anomaly worth investigating.
Response: The Incident Framework
When an attack is confirmed, speed is paramount. The NIST Incident Response Framework (widely adopted by South African Security Operations Centres) outlines a four-step lifecycle: Preparation, Detection/Analysis, Containment/Eradication and Recovery.
In the "Containment" phase, the priority is isolation. Automated systems should be configured to instantly sever the network connection of any infected device. This prevents the malware from spreading to file servers or cloud storage.
The South African Context: POPIA and Reporting
In South Africa, a ransomware attack is not just an operational crisis; it is a legal one. Under the Protection of Personal Information Act (POPIA), a ransomware incident where data is exfiltrated constitutes a data breach.
Organisations are legally required to notify the Information Regulator and the affected data subjects "as soon as reasonably possible". Failing to do so can result in significant fines and reputational damage. This makes forensic accuracy essential, as you need to know exactly what was stolen to report it accurately.
Building Resilience
Ultimately, resilience comes from preparation. This includes maintaining immutable offline backups (which malware cannot encrypt) and regularly testing your Incident Response Plan.
For those looking to lead these defence strategies, the Postgraduate Diploma in Information Technology (PDIT) at the Central University of Technology provides the advanced technical and management skills required to oversee complex security operations.
FAQs: Ransomware Attacks
1. Should we pay the ransom if our data is encrypted?
The general advice from cybersecurity experts and South African law enforcement is no. Paying does not guarantee you will get your data back, and it funds future criminal activity. Furthermore, paying a ransom does not absolve you of your legal obligation to report the breach under POPIA.
2. How long does it take to detect a ransomware attack?
It varies. "Dwell time" (the time an attacker spends inside a network before being detected) can range from days to weeks. The goal of tools like EDR and SIEM is to reduce this to minutes or hours.
3. What is "double extortion" ransomware?
Double extortion is when attackers not only encrypt your data but also steal it. They threaten to release the sensitive information publicly if the ransom is not paid, putting pressure on victims even if they have backups.
4. Can antivirus software stop all ransomware?
No. Traditional antivirus software relies on "signatures" of known viruses. Modern ransomware changes its code constantly. This is why behaviour-based tools (like EDR) that look for suspicious actions rather than specific files are more effective.
5. Is a ransomware attack considered a data breach under POPIA?
Yes, if there are reasonable grounds to believe that personal information was accessed or acquired by an unauthorised person. Since modern ransomware often involves data theft (exfiltration), it typically triggers POPIA reporting requirements.




