Digital security is undergoing a fundamental architectural realignment. As organisations migrate critical workloads to dispersed environments, the traditional "castle-and-moat" model, where a network is protected by static hardware firewalls, is insufficient for the complexities of the Fourth Industrial Revolution (4IR). This evolution requires a shift towards a cloud-native cybersecurity architecture, a model prioritising elasticity, identity-centric trust and granular visibility.
Article outline
- The Evolution of the Digital Perimeter
- Hardware Appliances vs. Cloud-Native Architectures
- Zero Trust and SASE: Identity-Centric Defence
- Microsegmentation and Breach Containment
- The African Cyber-Threat Landscape
- Professional Education: Building the Architecture of Defence
- Conclusion
- Frequently Asked Questions
FAQs
- How does a cloud-based firewall differ from a traditional hardware firewall?
- What is the primary role of microsegmentation in cloud security?
- Why is Zero Trust essential for the modern South African workforce?
- What are the main benefits of a SASE framework?
- How does the CUT Postgraduate Diploma in IT address current industry needs?
Related articles
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
The Evolution of the Digital Perimeter
Historically, enterprise security was anchored in physical appliances. For a South African corporation, the primary line of defence was a hardware firewall at the local area network (LAN) edge, serving as a gatekeeper for traffic. However, the advent of mobile connectivity and cloud migration has dissolved this boundary. In South Africa, where a 2025 report found that 93% of the workforce uses mobile applications like WhatsApp for professional communication, data flows between on-premise servers, multi-cloud platforms and remote endpoints. This has created an expanding attack surface where every device is a potential entry point.
The perimeterless environment now requires an approach where security is delivered as a modular, interoperable service rather than a monolithic physical barrier.
Hardware Appliances vs. Cloud-Native Architectures
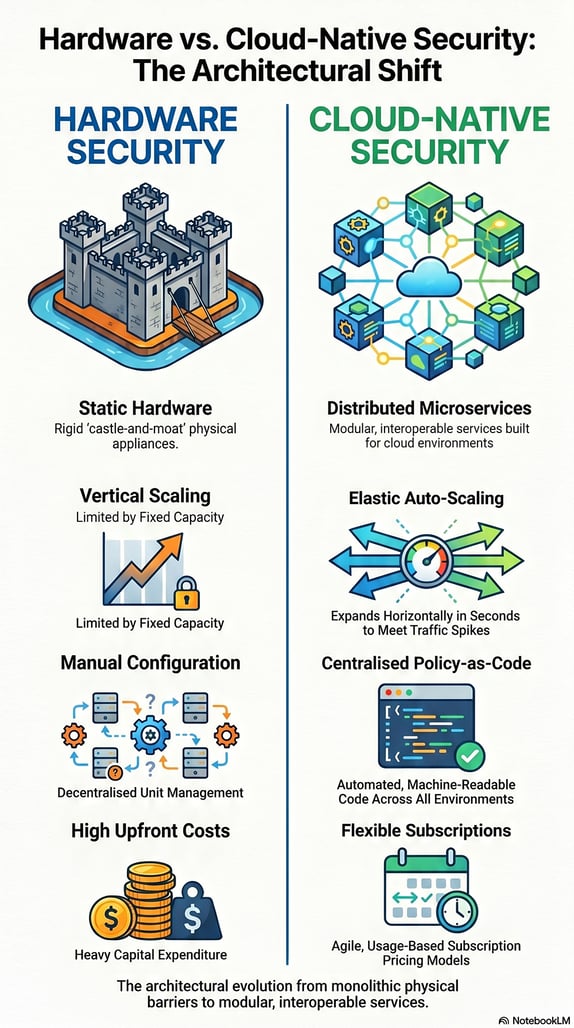
The distinction lies in engineering philosophy. Hardware firewalls are dedicated appliances designed for fixed physical boundaries, often resulting in rigid capacity constraints and high capital expenditure. In contrast, a cloud-native cybersecurity architecture is built specifically for the cloud using microservices and API-driven automation.
A cloud-based firewall, delivered as a service, operates as a distributed enforcement point that adapts to workload demands. This horizontal scalability allows for near-limitless elasticity, so that more server capacity becomes available when traffic spikes.
|
Metric |
Hardware Firewall |
Cloud-Native Security (CNF) |
|
Scaling |
Vertical (fixed hardware) |
Horizontal (elastic auto-scaling) |
|
Deployment |
Days/Weeks (shipping/install) |
Seconds (automated via API) |
|
Management |
Decentralised unit configuration |
Centralised Policy-as-Code |
|
Cost |
High upfront cost |
Flexible subscription cost |
Zero Trust and SASE: Identity-Centric Defence
The transition to cloud-native security is linked to Zero Trust Architecture (ZTA). Traditional models relied on "implicit trust" once a user enters a network, but this is a dangerous assumption in a landscape where identity theft and business email compromise are prevalent. Zero Trust treats every access request as untrustworthy until verified.
For the remote-first African workforce, Secure Access Service Edge (SASE) is an architectural model that converges networking with cloud-native security services. SASE eliminates the need to "backhaul" traffic through central data centres, a practice that often causes high latency, especially for users with limited bandwidth. By delivering security at the edge, SASE supports a modular security architecture that is as agile as the network it defends.
Microsegmentation and Breach Containment
Even with robust external defences, internal risks remain. Microsegmentation divides the network into isolated zones down to individual workloads. Unlike traditional segmentation, which filters "north-south" traffic (client-to-server), microsegmentation focuses on "east-west" communication between internal servers.
This is essential for limiting the "blast radius" of a breach. In the context of South Africa’s Protection of Personal Information Act (POPIA), microsegmentation allows organisations to cordon off sensitive customer data, applying granular policies to ensure only authorised processes interact with that information.
The African Cyber-Threat Landscape
The need for advanced architecture is underscored by evolving threats. South Africa receives the highest volume of threats on the continent, with 230 million incidents recorded in a single year. Despite this, a recent survey found that only 5% of South African organisations were classified as "Mature" in cybersecurity readiness.
Attackers are increasingly using generative AI for sophisticated phishing and fraud. Consequently, organisations must move toward proactive threat detection capabilities, including AI-driven anomaly detection and automated alerting.
Professional Education: Building the Architecture of Defence
The complexity of these systems requires a highly skilled workforce. The Postgraduate Diploma in Information Technology at the Central University of Technology (CUT) is designed to bridge this skills gap.
The curriculum covers advanced technical and leadership skills, including:
- Advanced Information Security: Strategies for perimeterless networks.
- Cloud Computing Platforms: Fundamentals of virtualisation and cloud service models.
- Ethical Hacking: Identifying and mitigating vulnerabilities.
- IT Governance and Compliance: Ensuring technical controls meet legal requirements like POPIA.
This two-year, fully online programme prepares IT professionals for leadership roles in overseeing complex digital transformations.
Conclusion
The shift from hardware firewalls to cloud-native security is the cornerstone of digital resilience in Africa. By adopting Zero Trust, SASE, microsegmentation, and investing in professional development, African enterprises can secure their shared digital prosperity in an increasingly volatile landscape.
FAQs: Cloud-Native Security
1. How does a cloud-based firewall differ from a traditional hardware firewall?
Hardware firewalls are physical appliances with fixed capacity limits, whereas cloud-based firewalls are software-defined, distributed solutions that scale elastically to meet real-time demand.
2. What is the primary role of microsegmentation in cloud security?
It isolates internal workloads to prevent lateral movement. If an attacker breaches one device, microsegmentation ensures they cannot easily access other critical systems or data.
3. Why is Zero Trust essential for the modern South African workforce?
With 93% of staff using mobile apps like WhatsApp for work, the perimeter has disappeared. Zero Trust ensures that every user is authenticated regardless of location.
4. What are the main benefits of a SASE framework?
SASE converges networking and security at the edge, reducing latency and complexity for distributed organisations by eliminating the need to backhaul traffic to a data centre.
5. How does the CUT Postgraduate Diploma in IT address current industry needs?
CUT's Postgraduate Diploma in IT provides advanced training in cloud platforms, cybersecurity measures, and ethical hacking, equipping professionals to lead architectural shifts in modern IT environments.




