The migration from on-premise data centres to the cloud has brought new challenges to the digital landscape in South Africa. As organisations scale, they no longer rely solely on physical firewalls and localised servers; instead, they depend on the complex, distributed protection of cloud provider cybersecurity architectures.
For local IT professionals, the challenge is twofold: mastering the technical architecture while navigating South Africa's strict regulatory framework regarding data sovereignty. In this article, we will take a look at how IT professionals can address these issues, with reference to the skills taught in CUT's fully online Postgraduate Diploma in Information Technology.
FAQs
- Does using a major cloud provider like AWS or Azure guarantee POPIA compliance?
- What is the difference between data residency and data sovereignty?
- How does a Zero Trust architecture differ from a VPN?
- Can South African companies legally store customer data on servers in Europe?
- What cloud security skills does the CUT PDIT programme cover?
Related articles
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
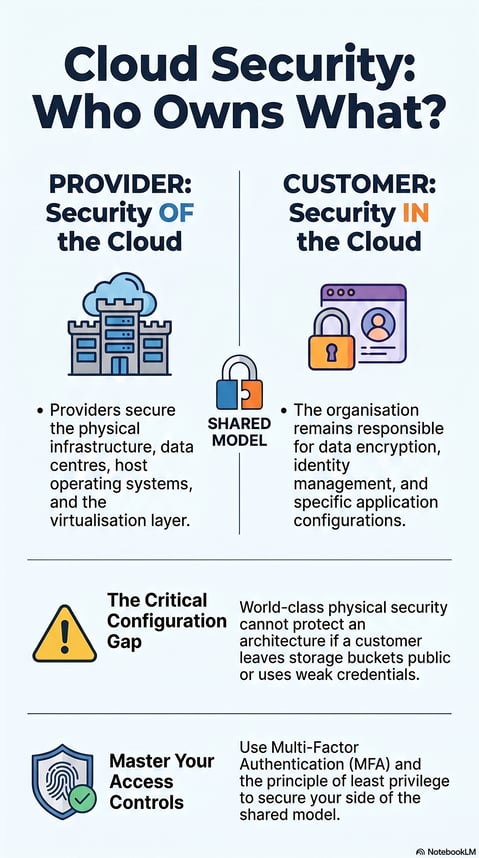
The Shared Responsibility Model
The cornerstone of cloud security is the Shared Responsibility Model. Unlike traditional IT, where the organisation owns every layer of the stack, cloud environments split the burden of defence.
- The Provider's Role: Major cloud providers (such as AWS, Azure, and Google Cloud) are responsible for the security of their cloud services. This includes the physical infrastructure, host operating systems and the virtualisation layer.
- The Customer's Role: The organisation is responsible for cloud security. This covers data encryption, identity management and application configuration.
Ignoring this distinction is a common vulnerability. A provider may offer world-class physical security at their Cape Town or Johannesburg data centres, but if a user leaves a storage bucket public or uses weak credentials, the architecture is compromised.
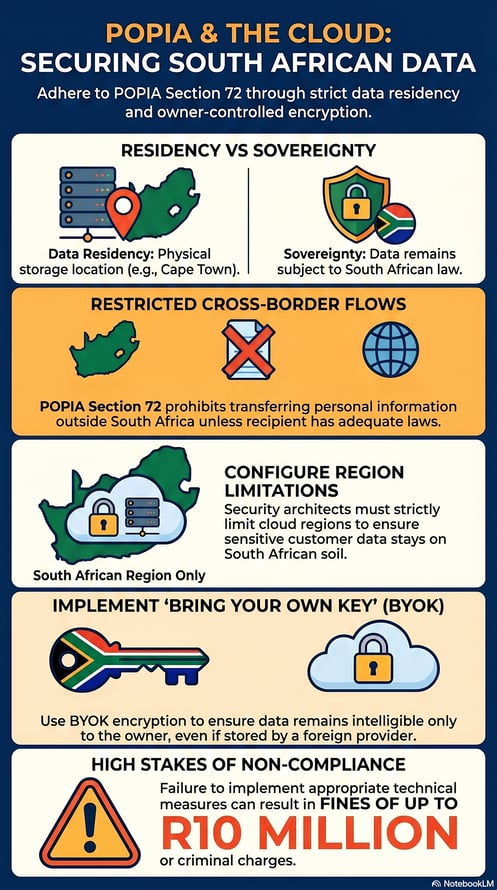
Navigating POPIA and Data Residency
In South Africa, cloud architecture cannot be designed in a vacuum; it must align with the Protection of Personal Information Act (POPIA) and the National Policy of Data and Cloud 2024. This is particularly pertinent when dealing with cross-border data flows. While major hyperscalers now have local regions, many services still default to routing data through US or EU servers.
POPIA Section 72 restricts the transfer of personal information outside South Africa unless the recipient country has adequate data protection laws. Security architects must therefore ensure that their cloud configurations enforce data residency. This involves:
- Strictly configuring region limitations to ensure sensitive customer data remains on South African soil.
- Implementing "bring your own key" (BYOK) encryption to ensure that even if data moves, it remains intelligible only to the data owner, not the foreign provider.
Embracing Zero Trust
Traditional network security operated on a "castle and moat" philosophy: once you were inside the network, you were trusted. In the cloud, where users access resources from anywhere, this model is obsolete. Modern cloud architectures increasingly rely on zero trust security architectures.
This framework assumes that no user or device is automatically trusted, even if already inside the network perimeter. Instead, every access request is authenticated, authorised and encrypted. By verifying identity at every touchpoint, cloud environments can limit lateral movement. If an attacker breaches one container or application, the zero-trust protocols prevent them from easily moving to others, containing the damage.
Security at Scale
The primary advantage of the cloud is scalability, but this introduces complexity. Managing security for a handful of servers is vastly different from securing thousands of dynamic containers. Automated cybersecurity systems at scale use Infrastructure as Code to embed security policies directly into the deployment process. This ensures that every new resource spins up with the correct security configurations automatically, reducing the risk of human error.
Cloud provider cybersecurity architectures offer immense power and flexibility, but they require a sophisticated understanding of modern defence strategies and local regulatory requirements. From mastering the Shared Responsibility Model to ensuring POPIA compliance, today’s IT leaders must be equipped to navigate this evolving terrain.
For professionals looking to deepen their technical expertise and strategic understanding of these systems, the Postgraduate Diploma in Information Technology (PDIT) at the Central University of Technology offers a comprehensive curriculum designed for the modern digital economy.
FAQs: Cloud Cybersecurity
1. Does using a major cloud provider like AWS or Azure guarantee POPIA compliance?
No. Under the Shared Responsibility Model, the provider ensures the security of the infrastructure, but you are responsible for how you store and process personal data within that infrastructure. You must configure access controls and encryption to meet POPIA standards.
2. What is the difference between data residency and data sovereignty?
Data residency refers to the physical location where data is stored (e.g., a data centre in Cape Town). Data sovereignty refers to the principle that data is subject to the laws of the country where it is located. Keeping data in South Africa ensures it remains under South African legal jurisdiction.
3. How does a Zero Trust architecture differ from a VPN?
A VPN generally trusts users once they are "inside" the private network. Zero Trust assumes no trust, even for users inside the network, and verifies every single request for access to a specific file or application.
4. Can South African companies legally store customer data on servers in Europe?
Yes, provided specific conditions are met. POPIA allows cross-border transfers if the recipient country has data protection laws similar to POPIA (such as the EU's GDPR), or if there is a binding agreement that ensures adequate protection.
5. What cloud security skills does the CUT PDIT programme cover?
The PDIT covers advanced topics including network security, cloud architecture defence, and the strategic management of information technology, preparing students to design secure systems at an enterprise level.




