The rapid increase of cloud-native infrastructure and mobile services has, unfortunately, seen South Africa become a primary target for sophisticated cyber-adversaries. As traditional network perimeters become porous, the implementation of advanced cybersecurity technologies is now an operational necessity. Modern threat detection is a continuous process of visibility and response facilitated by a synergistic layer of tools: Security Information and Event Management (SIEM), Endpoint Detection and Response (EDR), Network Detection and Response (NDR) and Intrusion Detection and Prevention Systems (IDS/IPS).
Related articles
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
South Africa's Imperative for Detection
The 2024 and 2025 assessments from Interpol and the South African Banking Risk Information Centre reveal a significant evolution in criminal tradecraft. While total financial crime losses in South Africa fell to R2.7 billion in 2024, digital banking fraud incidents more than doubled to 64,000 cases. This indicates that while preventative controls intercept bulk attacks, successful intrusions are more targeted and harder to identify. The rise in AI-driven social engineering and high-profile breaches at public entities like Statistics South Africa (Stats SA) underscores the need for a deep technical understanding of how SIEM, EDR, and NDR technologies safeguard the integrity of data systems.
IDS and IPS: The First Layer
The historical foundation of network security lies in Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS). These systems monitor activities for malicious patterns or policy violations.
An IDS functions as a passive sensor that monitors traffic without interference, alerting analysts to potential forensic indicators. Efficacy is measured by its detection rate (DR) and false-positive rate (FPR); a high FPR can lead to alert fatigue, where critical warnings are lost in noise.
Positioned in-line, an IPS can drop malicious packets or reset connections in real-time. Modern solutions utilise signature-based detection for known malware and statistical anomaly detection to identify deviations from "normal" behaviour.
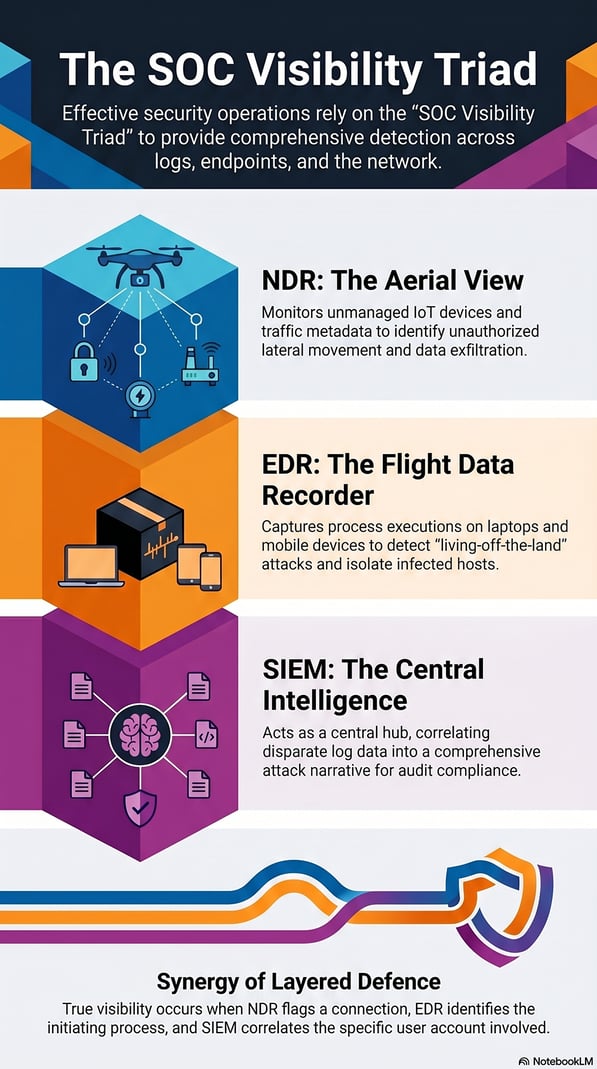
SIEM: The Central Intelligence
While IDS/IPS focus on individual streams, Security Information and Event Management (SIEM) provides macro-level visibility. A SIEM acts as a centralised repository that ingests and correlates log data from disparate sources, such as firewalls, servers and other security tools.
The primary value of a SIEM is its correlation engine. It links seemingly unrelated low-level events into a comprehensive attack narrative. Beyond detection, the SIEM is vital for compliance with the Protection of Personal Information Act (POPIA), providing the audit trails required to prove due diligence.
EDR and NDR: Endpoint and Aerial Visibility
With the South African workforce increasingly remote, "endpoints" (laptops and mobile devices) sit outside traditional perimeters. Traditional antivirus software often fails against "living-off-the-land" (LotL) techniques that make use of existing system functions and processes that would not normally be flagged. EDR addresses this by acting as a "flight data recorder", capturing process executions and registry changes to detect indicators of attack (IOAs).
When a threat is identified, EDR can automatically contain it by isolating the host, preventing the lateral movement common in ransomware campaigns.
Complementing this, NDR provides the "aerial view". NDR is platform-agnostic, monitoring unmanaged Internet of Things (IoT) devices that cannot host security agents. By applying machine learning to network metadata, NDR detects anomalies such as unauthorised data exfiltration that might bypass endpoint-focused tools.
The SOC Visibility Triad
No single tool is absolute. Effective operations utilise the "SOC Visibility Triad" integrating SIEM, EDR, and NDR technologies to provide layered defence. This synergy allows analysts to construct a comprehensive narrative: an NDR alert flags a suspicious connection, EDR identifies the initiating process, and SIEM correlates the user account involved.
Bridging the 2026 Skills Crisis: The CUT PDIT
Despite the power of these tools, their effectiveness depends on skilled human operators. By early 2026, the cybersecurity skills gap in South Africa had evolved into a structural crisis. Africa currently faces over 200,000 unfilled cybersecurity roles, and local demand for experts in AI-driven threat detection and cloud architecture continues to outpace the national supply of job-ready graduates.
The fully online Postgraduate Diploma in Information Technology at the Central University of Technology (CUT) is designed to address this deficit. The programme focuses on high-level theoretical engagement and practical specialisation, including:
- Advanced Information Security: Strategic management of SIEM and IDS frameworks.
- Ethical Hacking: Identifying vulnerabilities before they are exploited by malicious actors.
- Computer Architecture: Building the foundation to understand hardware-level threats and self-healing firmware.
By investing in high-level theoretical engagement and ethical hacking techniques, professionals ensure they are active defenders of the continent's digital future.
FAQs: Threat Detection
1. What is the difference between signature-based and behavioural detection?
Signature-based detection identifies known "fingerprints" of malware by looking at the code in files, while behavioural detection (used in EDR and NDR) identifies anomalies in activity, allowing it to catch new, "zero-day" threats. You can also read more about signature-based vs behavioural detection in a previous article.
2. Why is SIEM considered the "central hub" of a SOC?
SIEM is the only tool that aggregates and correlates data from every other layer (EDR, NDR and firewalls), providing a unified view of multi-vector attacks.
3. How does NDR protect unmanaged IoT devices?
Since IoT devices often cannot host security agents, NDR monitors the raw network traffic to and from these devices to detect unauthorised communications or signs of compromise.
4. Can EDR assist in forensic investigations?
Yes. EDR maintains a historical record of all host activities, allowing investigators to trace how an attacker gained access and what files were modified.
5. How do the CUT PDIT modules align with these technologies?
The Postgraduate Diploma in Information Technology includes modules like Advanced Information Security that covers the management of SIEM and IDS, while Ethical Hacking provides the "attacker’s mindset" needed to tune EDR and NDR systems effectively.




