Expanded connectivity and fintech innovation has led to the rapid growth of Africa’s digital infrastructure. However, this growth has been mirrored by an increasingly volatile security environment. In South Africa, traditional perimeter-based defences are proving insufficient against adversaries who exploit systemic vulnerabilities and the human element. Moving to a proactive, intelligence-driven security system requires mastering sophisticated frameworks. The Central University of Technology (CUT) addresses this through its Postgraduate Diploma in Information Technology, designed to equip IT leaders with the skills to operationalise frameworks like MITRE ATT&CK.
Article outline
Related articles
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
The Strategic Context in South Africa
South Africa possesses one of the most advanced cybersecurity ecosystems on the continent but remains the primary target for sophisticated attacks. In 2024, the country ranked first in Africa for cyber-incidents, with detections reaching 230 million. The average recovery cost for a single data breach in South Africa is now estimated at R49 million, reflecting technical restoration, regulatory penalties, and eroded public trust.
This environment necessitates a re-evaluation of the expanding attack surface, which now encompasses distributed cloud environments and mobile financial services.
Understanding the Taxonomy of Cyber Threats
To defend a network effectively, professionals must categorise the specific types of cyber threats defining the current era. These range from automated malware to targeted campaigns leveraging regional vulnerabilities.
- Ransomware: This remains the most disruptive threat. Hacker groups like Devman (accounting for 28.6% of regional activity) and Warlock target sectors like retail and technology using double-extortion models.
- AI-Driven Social Engineering: 2024 saw an escalation in AI-powered deepfakes and vishing (voice phishing) targeting vendors and C-suite executives.
- Advanced Persistent Threats (APTs): These are stealthy, long-term processes often orchestrated by state-sponsored actors to maintain network access, frequently using "Living off the Land" techniques to evade detection.
The Theoretical Foundations of CTI
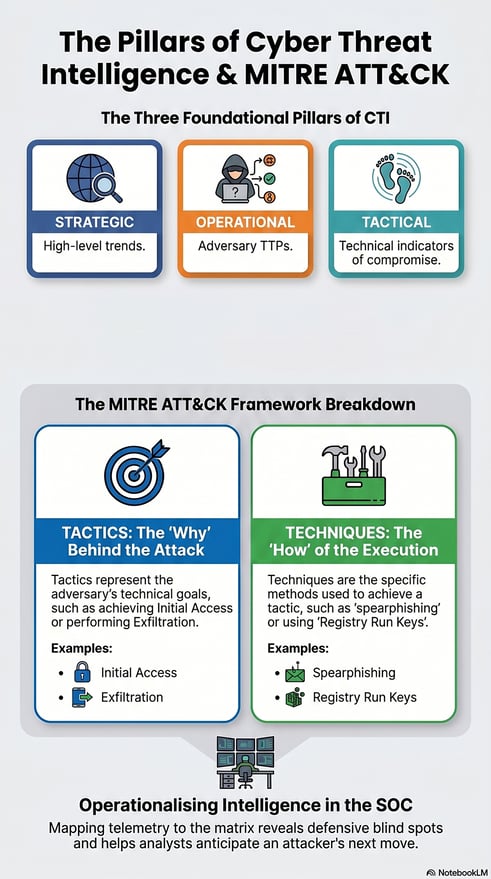
Cyber Threat Intelligence (CTI) is the process of analysing adversary information to inform defensive decisions. It turns raw data into actionable insights, moving beyond simple technical indicators to understand the "who, why, and how" of an intrusion. CTI is typically structured into three pillars:
- Strategic: high-level trends
- Operational: adversary tactics, techniques and procedures (TTPs)
- Tactical: technical indicators of compromise
The MITRE ATT&CK Framework: A Behavioural Shift
The MITRE ATT&CK Framework is a globally recognised knowledge base of adversarial behaviour based on real-world observations. It provides a common language for describing attack stages and focuses on post-compromise actions.
The matrix is structured around:
- Tactics: The adversary's technical goals (the "why"), such as Initial Access or Exfiltration.
- Techniques: The specific methods used to achieve a goal, like “spearphishing” or Registry Run Keys.
- Procedures: Real-world implementations and tools used by specific threat groups.
This behavioural focus offers far greater protection. While an attacker can easily change an IP address, their fundamental movement patterns are much harder and costlier to alter.
MITRE ATT&CK Threat Intelligence Integration
Effective MITRE ATT&CK threat intelligence integration involves mapping incoming telemetry to the matrix to reveal defensive blind spots. The methodology involves identifying observable behaviours, determining intent, and selecting the most specific technique ID.
Automation makes this much more effective, allowing for faster response times. Large Language Models (LLMs) and Natural Language Processing (NLP) can scan unstructured threat reports to automatically extract and map TTPs, reducing the burden on the people in Security Operations Centres (SOCs).
Operationalising the Framework in the SOC
For a SOC, the framework provides a blueprint for resilient detection. By aligning alerts with ATT&CK techniques, analysts can prioritise critical threats and conduct hypothesis-driven threat hunting. It also enables defensive gap analysis through "heat maps" that visualise where an organisation lacks visibility.
During the incident response lifecycle, the framework acts as an investigative roadmap, allowing teams to anticipate an attacker's next move and ensure that all persistence mechanisms are eradicated during recovery.
Academic Excellence: CUT’s PDIT Programme
The sophistication of these threats has created a critical skills shortage in South Africa. The CUT Postgraduate Diploma in Information Technology prepares graduates for these challenges through a career-focused curriculum.
Key modules include:
- Advanced Information Security: Focuses on risk assessment and policy design.
- Ethical Hacking: Provides the offensive perspective needed to master the ATT&CK framework.
- Advanced Research Project: Fosters intellectual independence in emerging fields like AI-driven detection.
Delivered 100% online, the programme allows South African professionals to advance their expertise without interrupting their careers.
FAQs: Cyber Threat Intelligence
1. How does mapping CTI to MITRE ATT&CK improve detection accuracy?
Mapping focuses on behavioural patterns rather than static indicators like IP addresses. By understanding the "why" (tactics) and "how" (techniques), teams can develop high-fidelity rules that catch novel or malware-free attacks while reducing false positives.
2. What is the difference between a Tactic and a Technique?
A Tactic is the adversary’s objective (e.g., Lateral Movement), while a Technique is the specific method used to achieve it (e.g., Remote Desktop Protocol). Sub-techniques provide even more granular implementation details.
3. Why should South African firms move beyond signature-based detection?
Signatures only catch known malware. Modern threats in the region, including APTs and ransomware, often use "Living off the Land" techniques that leverage legitimate system and which signature-based tools cannot identify.
4. How is the framework used for defensive gap analysis?
By mapping current security controls to the ATT&CK matrix, organisations create a visual "heat map" of their coverage. This reveals exactly which techniques an attacker could use undetected, allowing for prioritised investment in new logs or sensors.
5. How does MITRE ATT&CK support incident response?
It provides a structured roadmap to rebuild attack timelines. Responders can identify the current stage of a breach, anticipate the attacker’s next moves, and ensure that all persistence mechanisms are removed during eradication.




