The architectural framework of modern digital defence has shifted from the antiquated "castle-and-moat" paradigm toward a dynamic "sensory system" capable of identifying threats in real-time. As South Africa’s digital attack surface expands through cloud-native instances and mobile proliferation, the reliance on advanced detection mechanisms has become a cornerstone of national resilience. At the heart of this evolution is the distinction between signature-based and behavioural detection models. These two models can be integrated to form a robust hybrid framework.
Article outline
- The Sensory System: Threat Detection as First-Line Defence
- Signature-Based Detection: The Digital Fingerprint
- Strengths and Reliability
- Limitations and Evasion
- Behavioural Detection: The Intent-Based Paradigm
- Baselining and AI
- The Regional Context: South Africa’s Threat Landscape
- Hybrid Defence and Professional Competency
- FAQs
FAQs
- Why is signature-based detection still used if it cannot stop zero-day attacks?
- How does behavioural detection differentiate between a legitimate user and a hacker?
- What are the common reasons for false positives in behavioural systems?
- What role does "sandboxing" play in behavioural analysis?
- How does the PDIT programme specifically address these technologies?
Related articles
This article forms part of a larger series of articles on cybersecurity. You can use the index below to view any articles that interest you.
- Main article: The Architecture of Defence: How Cybersecurity Protects Networks
- Cloud Provider Cybersecurity Architectures
- Ransomware Attack Detection and Response
- Financial Sector Threat Detection Models
- The Expanding Attack Surface in Modern IT
- Why Cybersecurity Must Evolve to Counter Modern Threats
- From Hardware Firewalls to Cloud-Native Security Architectures
- How Threat Detection Works in Cybersecurity Systems
- Behavioural vs Signature-Based Detection: Cybersecurity
- Core Threat Detection Technologies (SIEM, EDR, NDR, IDS/IPS)
- Cyber Threat Intelligence and MITRE ATT&CK Mapping
- The Incident Response Lifecycle Explained
- SOAR Platforms and Automated Response
- Forensic Analysis and Root-Cause Investigation
- Incident Response Frameworks (NIST, ISO/IEC 27035)
- Security Management in Enterprise IT Systems
- Security Operations Centres (SOC & SOC-as-a-Service)
- Access Control, Identity Management, and MFA
- Cybersecurity Frameworks and Compliance Standards
- Service-Oriented Architecture in Cybersecurity
- Core Cybersecurity Services (IDaaS, TIaaS, IRaaS)
- Benefits of Modular and Interoperable Security Services
- SOA Challenges: Vendor Lock-In & Data Sovereignty
The Sensory System: Threat Detection as First-Line Defence
In a modern architecture of defence, threat detection serves as the primary intelligence-gathering layer. This system aims to rapidly identify known malicious entities while proactively discovering novel, previously unseen adversarial tactics. Understanding how threat detection works is essential for managing "alert fatigue" through automated alerting and prioritisation, allowing analysts to focus on high-risk movements mapped to frameworks like MITRE ATT&CK.
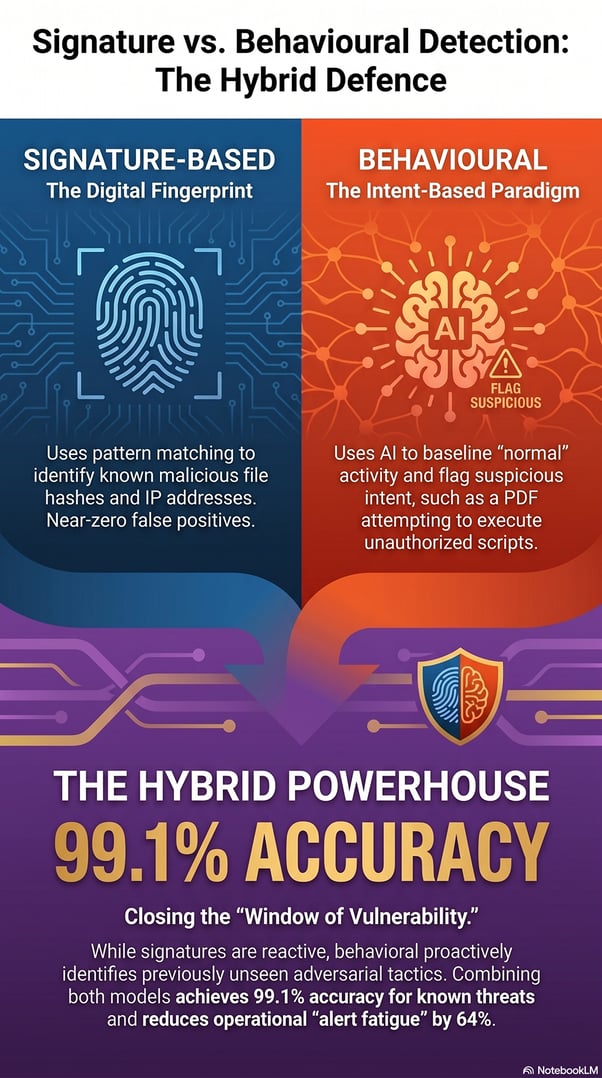
Signature-Based Detection: The Digital Fingerprint
Signature-based detection remains a historically significant component of the cybersecurity arsenal. It operates via pattern matching, comparing incoming data against a database of known malicious identifiers or "digital fingerprints". These signatures include file hashes, specific IP addresses, or unique byte sequences.
Strengths and Reliability
The primary advantage of this model is its speed and its near-zero false-positive rate for known threats. It is exceptionally efficient at filtering "commodity malware", which are widely distributed, non-customised threats that seek easy vulnerabilities. Because it requires light CPU and RAM resources, it serves as an excellent foundational baseline for basic digital hygiene.
Limitations and Evasion
Signature-based malware detection is inherently reactive. A signature can only be created after a threat has been discovered and analysed. This creates a "window of vulnerability" that attackers exploit using:
- Polymorphism: Malicious code that changes its appearance with each infection.
- Obfuscation: Hiding intent within layers of complex, nonsensical code.
- Encryption: Preventing scanners from seeing instructions until the code executes in memory.
Behavioural Detection: The Intent-Based Paradigm
To address these gaps, industry leaders have moved toward behavioural detection. Instead of asking what a file looks like, behavioural detection asks how it acts.
Baselining and AI
This model establishes a baseline of "normal" behaviour for users and devices through User and Entity Behaviour Analytics (UEBA). Deviations, such as unusual login locations or a PDF attempting to execute a PowerShell script, trigger immediate alerts. Modern systems rely on Artificial Intelligence (AI) and Machine Learning (ML) to sift through terabytes of data, identifying subtle correlations that human analysts might miss.
The Regional Context: South Africa’s Threat Landscape
The need for sophisticated detection is evidenced by statistics from the South African Banking Risk Information Centre. In 2023, digital banking fraud in South Africa surged by 45%, leading to losses of nearly R3.3 billion. Banking app fraud, in particular, saw an 89% year-on-year increase. Furthermore, the 2021 Transnet ransomware attack demonstrated how detection blind spots in critical infrastructure can lead to cascading economic consequences, including an estimated R50 billion in losses for the mining and agricultural sectors.
Hybrid Defence and Professional Competency
Research shows that hybrid models that combine signature-based speed with behavioural intelligence achieve up to 99.1% accuracy for known threats and 94.3% for zero-day attacks. Organisations implementing these architectures report a 64% reduction in false positives.
To lead these complex environments, the fully online Postgraduate Diploma in Information Technology (PDIT) offered by the Central University of Technology (CUT) provides critical training. This two-year, part-time online qualification includes modules such as:
- Advanced Information Security: Focused on risk assessment and encryption.
- Ethical Hacking: Teaching the "hacker mindset" to proactively identify vulnerabilities.
- Operating System Programming: Providing the deep technical understanding required to interpret anomalies at the kernel level.
By blending global best practices with African experience, the PDIT ensures graduates possess the intellectual independence to protect South Africa’s digital economy from evolving threats.
FAQs: Cybersecurity Detection
1. Why is signature-based detection still used if it cannot stop zero-day attacks?
It remains vital for operational efficiency. It is the fastest method for blocking millions of "commodity" threats that are already catalogued. By filtering this background noise instantly, it allows more resource-intensive behavioural engines to focus on novel, complex threats.
2. How does behavioural detection differentiate between a legitimate user and a hacker?
It uses UEBA to establish a baseline for "normal" behaviour. If a user suddenly logs in from an unusual IP address, modifies a large number of files, or accesses sensitive data outside regular hours, the system flags the action as inconsistent with that user's history, even if they have the correct credentials.
3. What are the common reasons for false positives in behavioural systems?
False positives often occur during the "learning phase" when legitimate changes, such as a scheduled server update or an employee working late on a special project, are mistaken for malicious deviations from the established baseline.
4. What role does "sandboxing" play in behavioural analysis?
A sandbox is a safe, isolated virtual environment where a suspicious file is executed. A behavioural engine observes its actions (e.g., attempting to encrypt files or contact a command-and-control server) to confirm malicious intent without risking the production network.
5. How does the PDIT programme specifically address these technologies?
The online Postgraduate Diploma in Information Technology programme features dedicated modules in Advanced Information Security and Ethical Hacking. These modules teach students how to design secure architectures and how to proactively hunt for threats by identifying the very vulnerabilities that bypass traditional signature-based systems.




